AIM Documentation
Open-source agent identity management. Pick a setup and start securing your agents.
What is AIM?
AIM (Agent Identity Management) provides cryptographic identity for AI agents. Every agent gets an Ed25519 key pair that uniquely identifies it, enabling verifiable signatures on actions, tamper-evident audit logs, and capability-based access control. AIM answers the question: "Which agent did what, when, and was it authorized?"
Identity
Ed25519 key pairs for every agent. Verify who is making requests.
Audit
Tamper-evident log of every action. Full traceability for compliance.
Policy
Capability-based access control. Agents only do what they are allowed to.
Trust
8-factor trust scoring. Dynamic risk assessment based on behavior.
Install via CLI
npm install -g opena2a-cliThe OpenA2A CLI includes AIM commands for identity creation, trust scoring, and agent security scanning. Run opena2a identity create --name my-agent to generate your first agent identity.
1. Choose your setup
AIM Platform
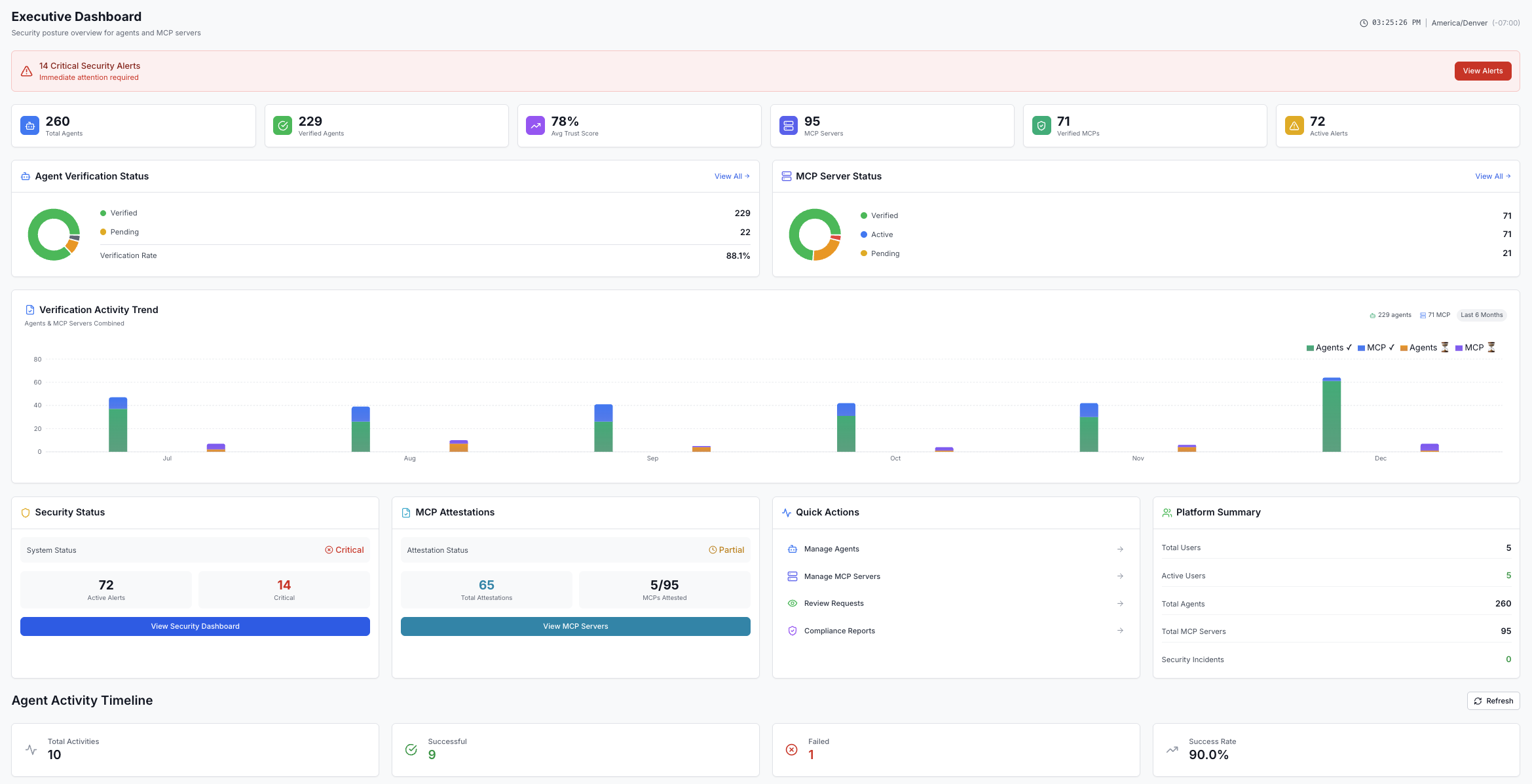
Dashboard, fleet management, RBAC, compliance reporting, cross-agent analytics. Requires Docker.
docker compose up -d@opena2a/aim-core
No serverEd25519 identity, capability policy, trust scoring, and audit log in a single npm package. No infrastructure.
npm install @opena2a/aim-core2. Pick your path
Python Developer
Secure agents with the Python SDK. LangChain, CrewAI, and Anthropic/OpenAI integrations.
Java Developer
@SecureAction annotations, Spring Boot integration, and LangChain4j support.
Security Engineer
Trust scoring, security policies, alerts, and compliance reporting.
Platform Admin
Installation, user management, API keys, audit logs, and dashboard setup.
3. Key concepts
Trust Scoring
8-factor algorithm for dynamic risk assessment
MCP Servers
Register and verify MCP servers with security policies
REST API
Complete API reference with request/response examples